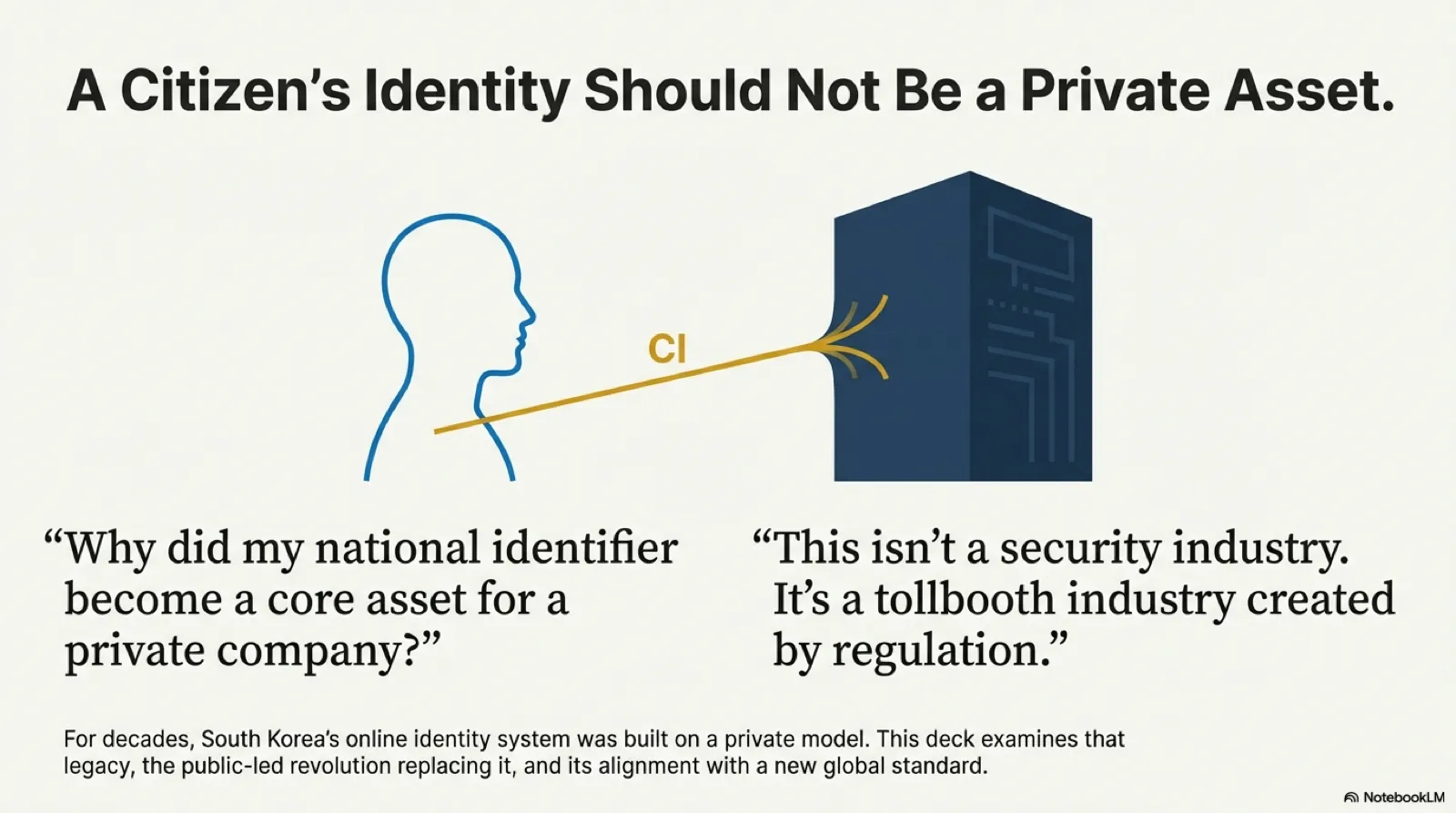
Why Account Takeover Never Ends — Dismantling the ATO Supply Chain
How Korea’s CaaS supply chain reproduces itself through the recycling loop of points, gift cards, and crypto — and why defending against it requires reading the entire behavioral network, not just the login page.