AI IDEs, MCP, and automation connectors are not merely convenience tools. They are supply-chain assets that change the trust path of the development process.
This is the fourth article in the Beyond CVE Security series.
- Part 1: Beyond CVE Response: AI-Era Vulnerabilities Move Before They Get Numbers
- Part 2: The AI Slop Paradox: Why Triage Gets Harder When Vulnerabilities Get Easier to Find
- Part 3: Security Assessment Becomes a Development Process, Not an Outsourced Event
- Part 4: Supply Chain Security Does Not End with SBOM: Governing AI Development Tools and Automation Connections
The earlier articles covered the limits of CVE/NVD-centered response, AI slop and triage cost, and the shift in security assessment operating models. This final article expands supply-chain security to AI development tools, MCP, automation connections, and developer-environment governance.
1. We Have Been Defining Supply Chain Too Narrowly
When people hear supply-chain security, they often think first about open source libraries.
Which package do we use?
Which version?
Is there a known vulnerability?
Is the license acceptable?
Do we have an SBOM?
Those questions still matter. But they are no longer enough.
The development environment is changing.
Developers no longer use only an IDE and terminal. They use AI IDEs, coding assistants, MCP-based connections, issue tracker integration, repository integration, document search, CI/CD status access, and security-result summarization.
These tools do not remain simple convenience features. They influence code changes, review requests, issue cleanup, test interpretation, and deployment preparation.
A tool that influences code production is part of the supply chain.
2. SBOM Is a Starting Point, Not the End
SBOM is important.
If an organization does not know which libraries and packages it uses, it cannot judge vulnerability impact. Even after a CVE is published, response is delayed when internal usage is unknown.
But SBOM mainly describes software components. By itself, it does not describe the full trust path of development and deployment.
For example, SBOM alone cannot answer:
- Which teams use which AI development tools?
- Which internal systems do those tools connect to?
- Who manages and approves MCP-based connections?
- What review process applies to changes generated by development tools?
- How do automation results flow into repositories, issue trackers, and build pipelines?
- Who reviews and records tool configuration changes?
- How traceable are automated activities inside developer environments?
Those are supply-chain questions.
They are just not visible in a traditional SBOM-centered model.
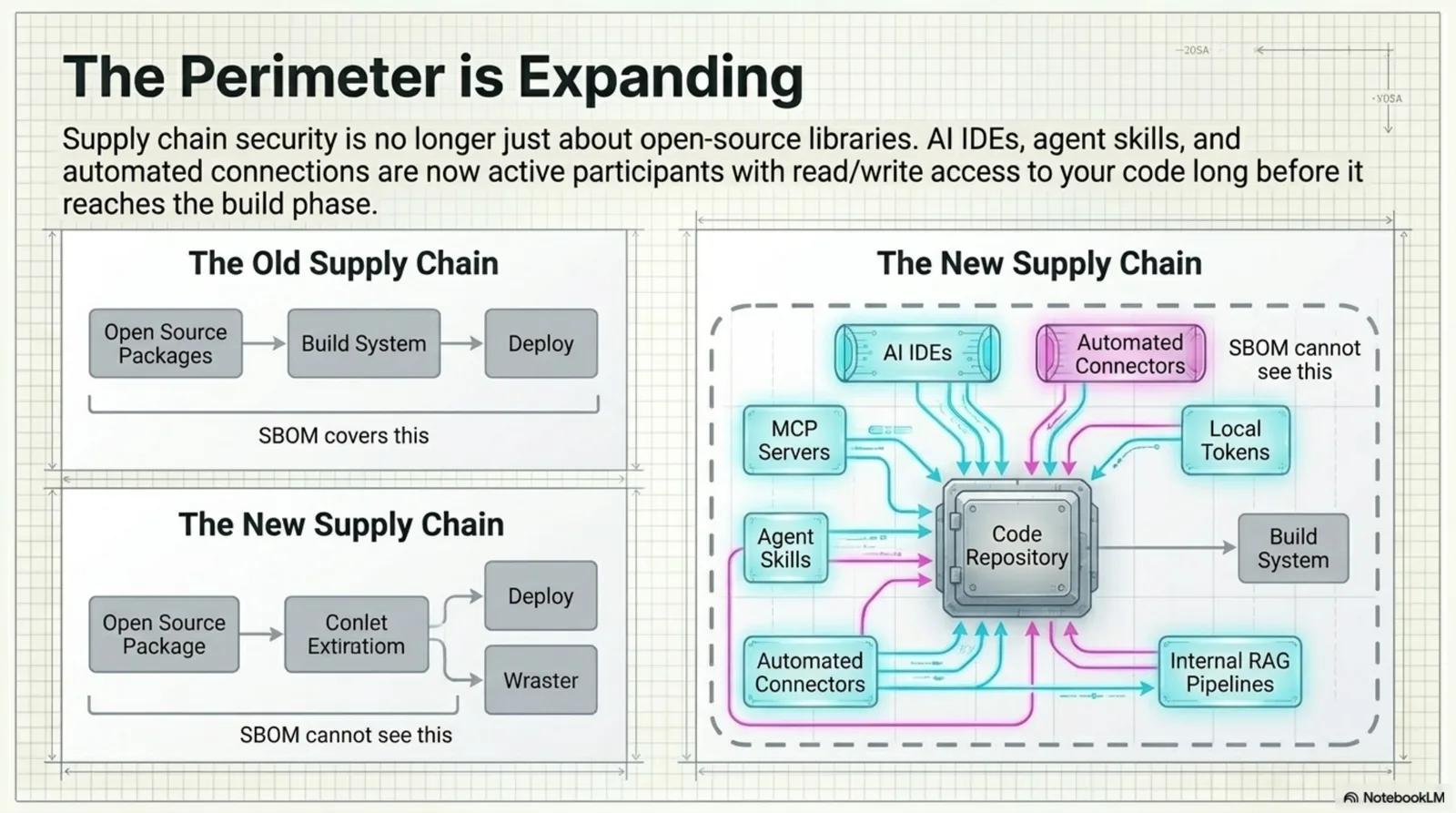
Figure. The old supply chain covered open source packages, build systems, and deployment. The new supply chain also includes AI IDEs, MCP servers, agent skills, automated connectors, local tokens, and internal RAG pipelines.
3. AI Development Tools Are New Workflows
Early AI coding tools were mostly autocomplete and explanation.
- code completion
- function explanation
- test draft generation
- refactoring suggestions
- documentation drafts
Newer tools enter a broader workflow.
- They suggest multi-file changes.
- They read test results and explain failures.
- They connect issue descriptions to code changes.
- They write PR descriptions.
- They summarize review comments.
- They generate repeated checklists.
- They translate security findings into developer language.
This increases productivity. It also expands what security teams have to understand.
The question is no longer:
Do we use AI tools?
The better question is:
Which development workflows do AI tools participate in, and what review path turns their output into code or operations?
That question matters more.
4. MCP and Automation Connections Are Governance Targets
MCP and automation connections let AI tools work across multiple systems.
That structure is useful. Documentation, repositories, issue trackers, build status, and security test results can be read in one flow.
But every connection adds governance responsibility.
| Area | Governance Question |
|---|---|
| connection scope | Which systems are connected? |
| approval path | Who approves the connection and reviews changes? |
| role separation | Are read, propose, modify, and approve roles separated? |
| history | Which sources were used and what output was produced? |
| quality standard | How is generated output reviewed? |
| exception handling | How are high-risk changes or sensitive operations approved? |
| operational responsibility | Who owns failure, misuse, or quality degradation? |
The risk is not tied to one specific technology name.
The deeper risk is that unclear connections and unclear approval structures enter the development process.
MCP and automation connections should therefore be treated as governance objects, not only technical integration items.
5. Developer Environments Are Part of the Supply Chain
Traditional supply-chain security focused on central repositories, package registries, and build systems.
As AI development tools spread, developer environments become more important.
A developer environment may contain:
- source code
- branches and PR workflows
- internal documentation access
- issue trackers
- test scripts
- local configuration
- IDE extensions
- AI tool settings
- automation connection data
This environment is not just a workspace. It is where code is created, reviewed, and steered.
The developer environment is inside the supply chain, not outside it.
Securing only the central build system is not enough. Security teams also need to understand what tools operate in the developer workflow and how those tools affect decisions.
6. AI Development Tool Review Items
Completely banning AI development tools is not realistic.
The practical direction is to understand their usage structure and create safe defaults.
Review items can include:
| Review Item | Question |
|---|---|
| usage | Which teams use which AI development tools? |
| scope | Are they used for code, review, tests, docs, or issue management? |
| connected systems | Which repositories, issue trackers, docs, or CI/CD systems are connected? |
| change process | What review path applies to tool-generated changes? |
| approval criteria | Do high-risk changes require separate approval? |
| output quality | Is accuracy and re-review ratio measured? |
| history | Are major automation actions and reasons recorded? |
| exception management | Who approves team-level exceptions and how often are they reviewed? |
| education | Do developers understand tool limits and review responsibility? |
| cost visibility | Can usage and operating cost be measured by process? |
These items may not exist in traditional security checklists.
But the boundary between developer-environment security and supply-chain security is becoming less clear.
7. Before Least Privilege, Map the Trust Path
Least privilege is a core security principle.
But for AI development tools and automation connections, the trust path has to be visible first.
- What input does the tool read?
- What output does it generate?
- Who reviews the output?
- Where does a human approve it?
- Which output can affect repositories or deployment flow?
- How far can the organization roll back if something goes wrong?
If the path is invisible, privilege cannot be reduced intelligently.
The first task is not to block everything.
The first task is to map the trust path.
An organization should draw which systems AI development tools connect to, what they produce, and which process turns their output into code or operations.
Only then can it design permission scope, approval gates, logs, exception handling, and quality standards.
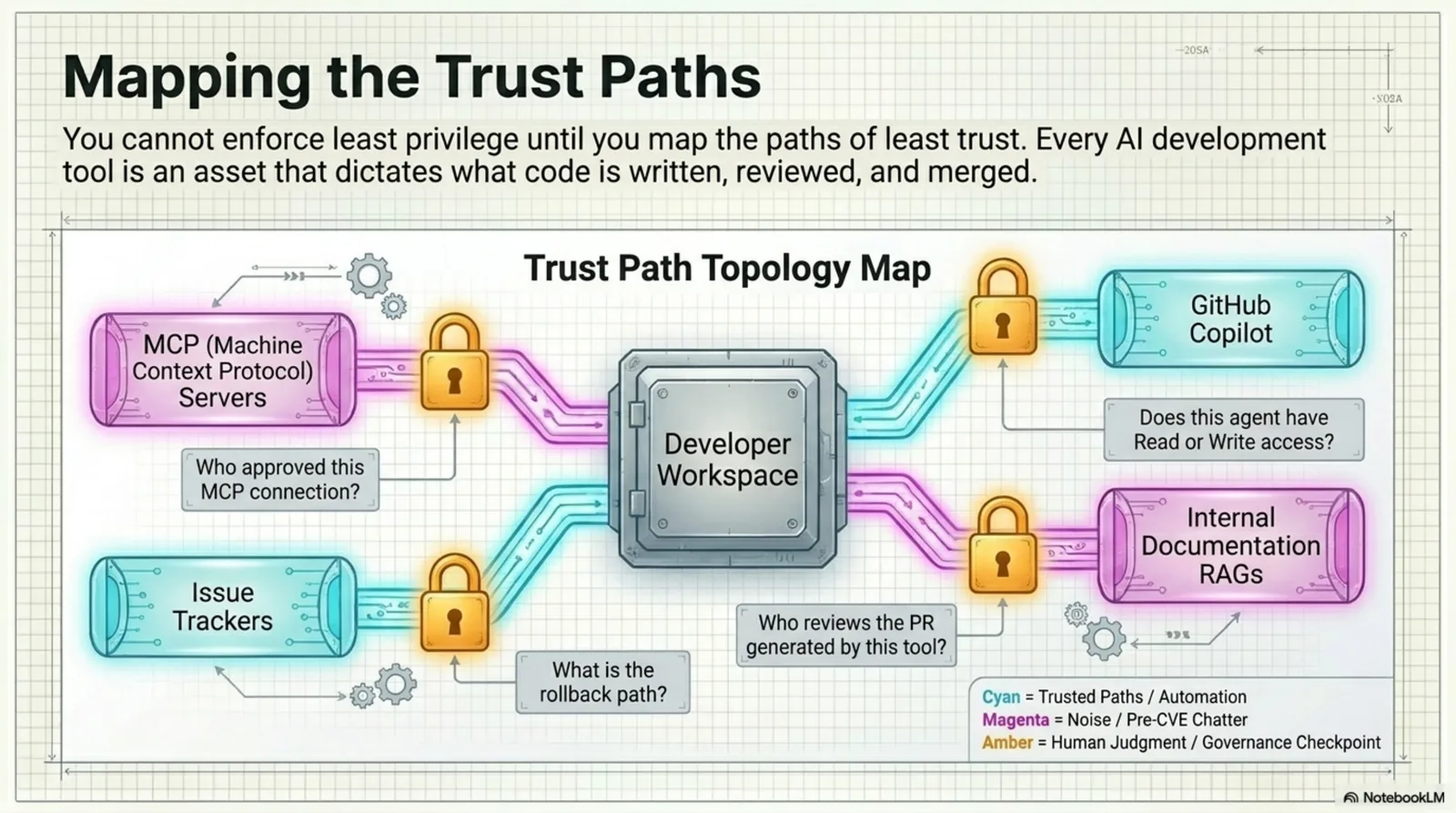
Figure. Least privilege becomes practical only after the trust path is visible: what the tool reads, what it proposes, where review happens, and where changes enter repositories or deployment pipelines.
8. Supply-Chain Response and Security Assessment Connect
The previous article argued that security assessment has to be embedded in the development process.
That does not simply mean adding SAST to CI/CD.
It means the object of security assessment becomes broader.
Future assessment needs to include:
- code vulnerabilities
- open source dependencies
- API exposure
- CI/CD configuration
- build scripts
- deployment procedures
- developer environments
- AI development tool settings
- MCP and automation connections
- issue-to-code change flow
- retest flow for security findings
From this view, supply-chain security and security assessment are not separate workstreams.
Supply-chain security becomes an input to assessment. Assessment becomes a repeatable verification system that reduces supply-chain risk.
9. Conclusion: AI Tools Are Assets
AI IDEs, MCP, and automation connections are not simple convenience tools.
They affect what developers decide, what code is written, and what review path code passes through.
Organizations therefore have to manage AI development tools as assets.
AI-era supply-chain security has to expand the question.
What software do we use?
becomes:
Which tools and connections have we delegated part of the development process to?
SBOM remains necessary. But SBOM is not enough.
What is needed now is a broader trust-path map that includes development tools, automation connections, approval paths, change history, and quality criteria.
AI-era supply-chain security is ultimately the work of mapping and governing trust paths inside the development process.
The output of this article is a trust-path map: identify AI tools and MCP connections as assets, then manage connection scope, approval paths, change history, and quality standards together.
The starting point does not have to be grand.
- List the AI IDEs, coding assistants, MCP servers, and automation connectors used in the organization.
- Classify what each tool reads, writes, and proposes.
- Do not combine read, propose, modify, and approve permissions as if they were one permission.
- Keep history for tool-generated changes and human-approved changes.
- Treat connections to high-risk repositories, deployment pipelines, and operational secrets as exceptions that require separate approval and periodic review.
Even this changes the question from “do we use AI tools?” to “which trust path has which authority?” Supply-chain security begins there.
To close the series, the core point is one operating model. Post-CVE waiting, same-depth triage for every candidate, one-time security assessment, and SBOM-only supply-chain management all share the same limit. In the AI era, signals move faster, candidates multiply, and development paths expand. Security can no longer wait for numbers, reports, and inventories. It has to become an operating system for continuously verifying trust paths inside development.
FAQ
Q1. Does this mean organizations should stop using AI IDEs or MCP?
No. The point is governance, not prohibition. Organizations need to know which tools connect to which systems, what output they produce, and what approval path turns that output into code or operations.
Q2. Should this really be part of supply-chain security?
Yes. The supply chain is not only open source packages. It includes the trust path through which code is written, reviewed, built, and deployed. AI development tools and automation connections are part of that path.
Q3. Where should an organization start?
Start with an inventory of AI development tools, MCP connections, and automation connectors. Then classify which systems each tool reads, writes, or proposes changes to. After that, define approval paths and change history requirements.
Start from the beginning: Beyond CVE Response: AI-Era Vulnerabilities Move Before They Get Numbers