AI-era vulnerability response cannot wait for a CVE number. Vulnerabilities now move through issues, commits, PoCs, write-ups, and patch traces before the official identifier arrives.
This is the first article in the Beyond CVE Security series.
- Part 1: Beyond CVE Response: AI-Era Vulnerabilities Move Before They Get Numbers
- Part 2: The AI Slop Paradox: Why Triage Gets Harder When Vulnerabilities Get Easier to Find
- Part 3: Security Assessment Becomes a Development Process, Not an Outsourced Event
- Part 4: Supply Chain Security Does Not End with SBOM: Governing AI Development Tools and Automation Connections
This series extends earlier arguments about CVE as shared security infrastructure and security testing as an executable process. The question now moves from identifiers to operations.
Related reading:
1. CVE Is Still Necessary
CVE is the common language of vulnerability response.
It lets scanners, vendors, advisories, threat intelligence, and internal patching processes refer to the same weakness with the same identifier. Without CVE, every tool and organization would name the same issue differently.
That means CVE is not just a number.
It is a coordinate system for the security ecosystem.
The problem is not that the coordinate system disappeared. The problem is that vulnerability discovery, reproduction, and public discussion are starting to move faster than the coordinate system can be completed.
CVE has not become irrelevant.
Because CVE is so important, we have to decide what to do before the number exists.
2. NVD Enrichment Is an Operational Bottleneck
Many vulnerability programs assume a familiar sequence.
CVE published -> NVD enrichment -> scanner detection -> prioritization -> patching
Here, enrichment means adding the operational metadata that tools and teams need after a CVE is created. A raw CVE entry may contain a description and references, but NVD enrichment adds fields such as CVSS, CPE mappings, and CWE classifications.
Those fields are not decorative.
- CVSS is often used as an initial severity signal.
- CPE mappings connect the vulnerability to products and assets.
- CWE helps classify the vulnerability pattern and root cause.
When enrichment is late or incomplete, the vulnerability may be known but poorly mapped. The security team still has to determine whether it affects internal assets, how urgent it is, and what pattern of weakness it represents.
That is not merely a data quality issue.
It is a vulnerability management bottleneck.
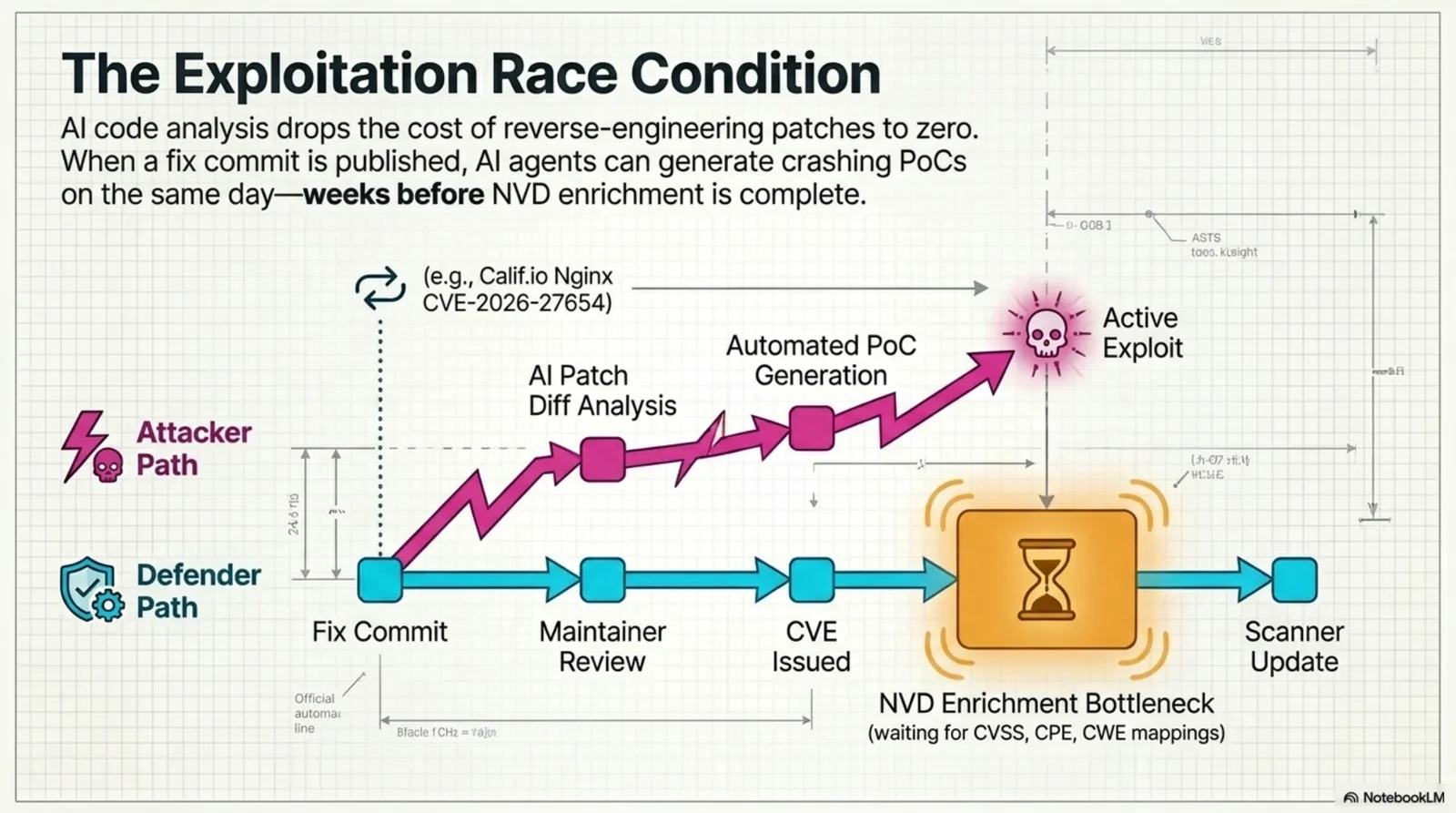
Figure. CVE remains a necessary coordinate system, but the exploit path can move faster than the defender path when NVD enrichment and scanner mapping lag behind.
3. AI Lowers the Cost of Vulnerability Discovery
The important change in AI-assisted vulnerability research is not that “AI hacks everything.”
The important change is that the cost of discovery and reproduction is falling.
Finding a vulnerability in a codebase, narrowing the conditions, checking the patch, and producing a working reproduction still requires expertise. But AI agents, code analysis models, and automated reproduction workflows reduce the amount of time needed for parts of that work.
Public examples already show this direction. Calif.io’s nginx CVE-2026-27654 write-up and califio/publications show a workflow where Claude helped identify suspicious conditions, humans validated exploitability, and disclosure was coordinated with the vendor. A more operationally important point is that an AI-based commit watcher reportedly generated a crashing PoC from a fix commit on the same day the patch appeared.
Trail of Bits’ AI-native operating model, Buttercup, and trailofbits/skills point in the same direction. AI is no longer only a report-drafting assistant. It is entering the workflow for finding candidates, interpreting fuzzing output, proposing patches, and narrowing what humans need to verify.
When cost falls, the effect is straightforward.
More people try.
More code gets analyzed.
More vulnerability candidates appear.
More PoCs and write-ups are produced.
Some of them are real. Some are exaggerated. Some are wrong. But defenders still have to separate them.
An era that finds more vulnerabilities is also an era that must triage more vulnerability candidates.
4. Vulnerabilities Move Before They Get Numbers
Vulnerability disclosure does not always follow a clean sequence.
discovery -> CVE assignment -> advisory -> patch -> operational response
In practice, the trail often looks different.
- A GitHub issue discusses suspicious behavior.
- A PR or commit looks like a security fix.
- A researcher blog or social post describes reproduction conditions.
- A fuzzing walkthrough contains a vulnerability hint.
- A maintainer does not initially classify the bug as a security issue.
- A PoC or exploit note circulates before CVE assignment.
AI adds speed to this path.
It can read a commit diff, compare the before and after code, infer the vulnerable condition, and draft reproduction code. That means attackers and researchers can obtain useful hints before an official advisory is complete.
The defender’s question changes.
Does this CVE affect us?
becomes:
Can this pre-CVE signal be exploited in our supply chain?
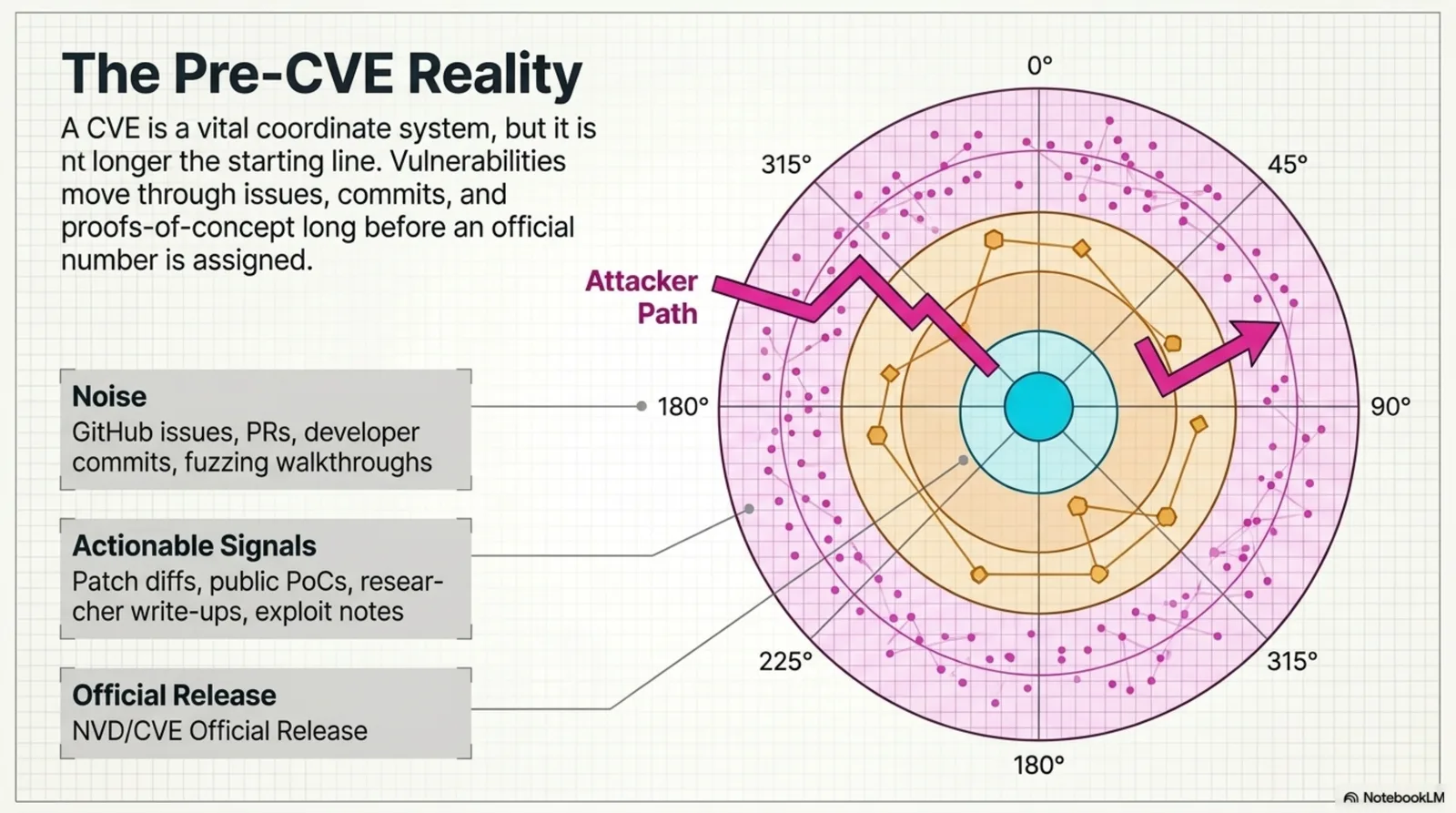
Figure. Issues, commits, write-ups, and PoCs can become actionable signals before official CVE release. The defender has to reason about exploitability earlier.
5. No-CVE Candidates Cannot Be Ignored
No CVE does not mean no vulnerability.
It may mean one of several things.
- Disclosure is still being coordinated.
- The maintainer has not responded.
- The security impact is disputed.
- The patch exists but the advisory does not.
- The issue is real but did not go through CVE assignment.
- A researcher recorded the finding in a public channel first.
For operations, the more important questions are concrete.
Do we use it?
Is it externally exposed?
Is there a PoC or exploit note?
Is there a patch commit?
Can it be reached without authentication?
Is it related to RCE, LPE, auth bypass, or memory corruption?
If the answer is yes, the candidate may deserve review even without a CVE number.
But treating every no-CVE candidate the same will exhaust the team. The answer is not more alerts. The answer is better triage.
6. The Supply Chain Feels the Pressure First
AI-assisted analysis puts early pressure on the software supply chain.
There are two reasons.
First, the supply chain is analyzable.
Open source packages, package registries, Docker images, CI/CD settings, build scripts, and deployment pipelines are relatively structured. Much of the code and configuration is public. That makes them suitable for repeated AI-assisted analysis.
Second, the blast radius is broad.
A single library, build action, package, or base image can affect many downstream services. If attackers can move from patch commit to exploit faster, downstream users may be exposed before the official vulnerability record is complete.
That is why pre-CVE response is not only a vulnerability management issue.
It is a supply-chain operations issue.
7. The Practical Response Model
A practical model starts with early signals, then maps them to internal exposure.
The minimum workflow looks like this.
collect pre-CVE signals
-> remove duplicates
-> map to internal SBOM and repositories
-> check external exposure
-> inspect patch commits and PoCs
-> evaluate exploitability
-> route to human verification
The goal is not to panic whenever a suspicious issue appears.
The goal is to avoid waiting passively for CVE, NVD, and scanner updates when the evidence already suggests that the organization’s supply chain may be exposed.
The response surface expands from public vulnerability feeds to the earlier traces around code, patches, and reproducibility.
8. Beyond CVE Security
“Beyond CVE” does not mean abandoning CVE.
CVE, NVD, KEV, GitHub Advisory, vendor advisories, and scanner data all remain necessary.
But the operating model has to extend.
post-CVE response
-> pre-CVE signal collection
-> internal supply-chain mapping
-> exploitability-based triage
-> human verification and action
The output of this article is an operating view: do not ignore pre-CVE signals, and do not treat them as confirmed vulnerabilities either. Map them against internal usage, exposure, and exploitability first.
This leads directly to the next problem.
If AI creates more vulnerability candidates, how do defenders avoid drowning in noise?
FAQ
Q1. Does this mean CVE and NVD are no longer useful?
No. CVE is still the common language of vulnerability response. The point is that waiting for CVE and NVD alone is no longer enough. CVE-based response should remain, but it needs to be complemented by pre-CVE signal handling.
Q2. Will no-CVE monitoring overload security teams?
It can. That is why the goal is not to investigate every no-CVE item equally. The first filter should be internal usage, external exposure, PoC availability, patch evidence, and high-risk vulnerability class.
Q3. Does AI fully automate vulnerability discovery now?
No. The important change is cost and speed, not full autonomy. AI can help find candidates, narrow reproduction conditions, and interpret patch diffs, but human validation remains necessary.
Next: The AI Slop Paradox: Why Triage Gets Harder When Vulnerabilities Get Easier to Find