Security controls already exist. The real problem is that we cannot decide which customer, at which moment, deserves how much friction. As the closing chapter of the CAPTCHA·ATO series, this post is about moving from quantity of controls to context of controls — adaptive security as an operational discipline.
Representative Foreword
After the Code, the Structure Remains
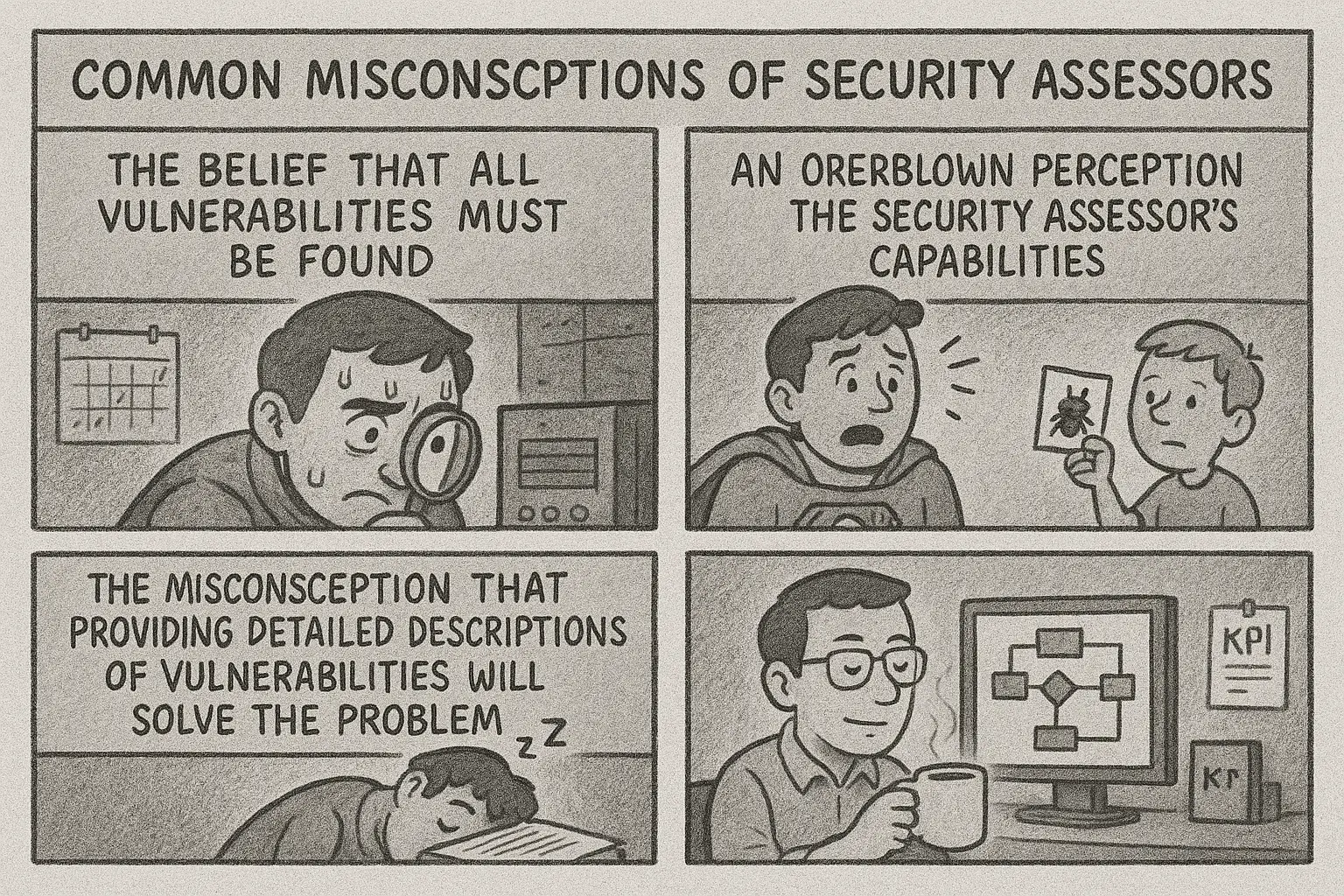
The representative foreword of this blog: security now fails less at finding issues than at absorbing, sustaining, and acting on what has already been found.
This essay frames the entire site first. The posts on technical analysis, method, and governance all start from this same problem statement.
Detection, Method, Governance
🔥 A Mind That Dissects Systems
🔥 Trust and Culture Beyond Technology
🔥 Code That Fixes, Not Just Runs
Why Security Knowledge Transfer Fails — and What to Design Instead
An organizational design report that reframes the security–DevOps problem from failed knowledge transfer to default design, interfaces, exception handling, and alignment.
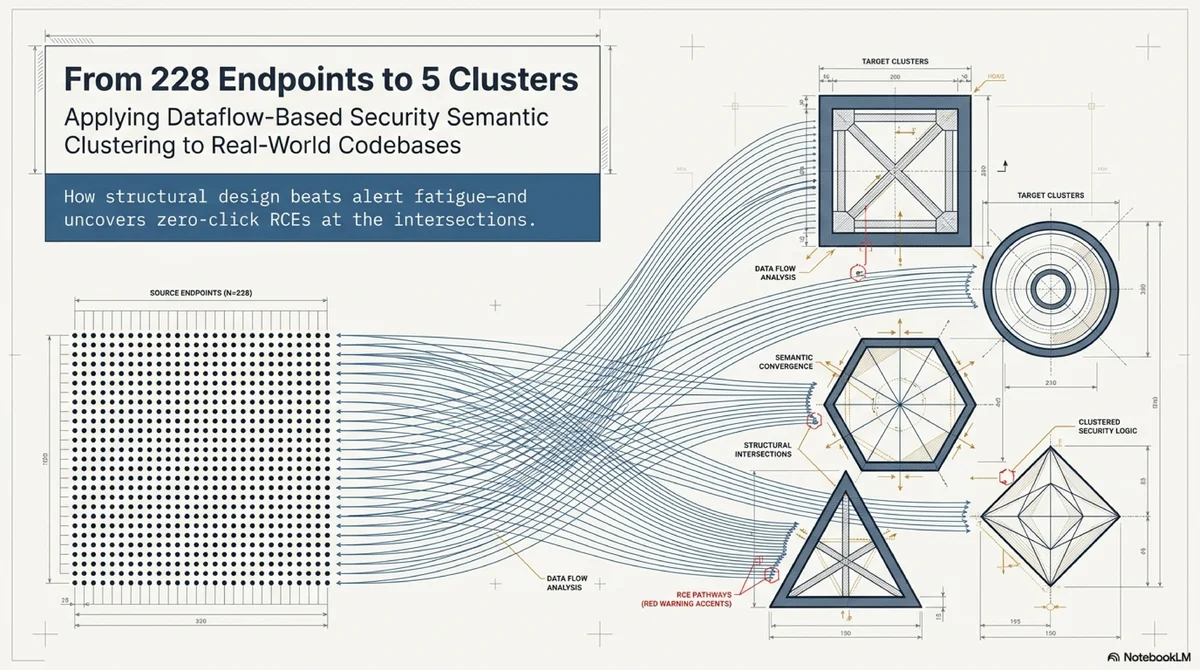
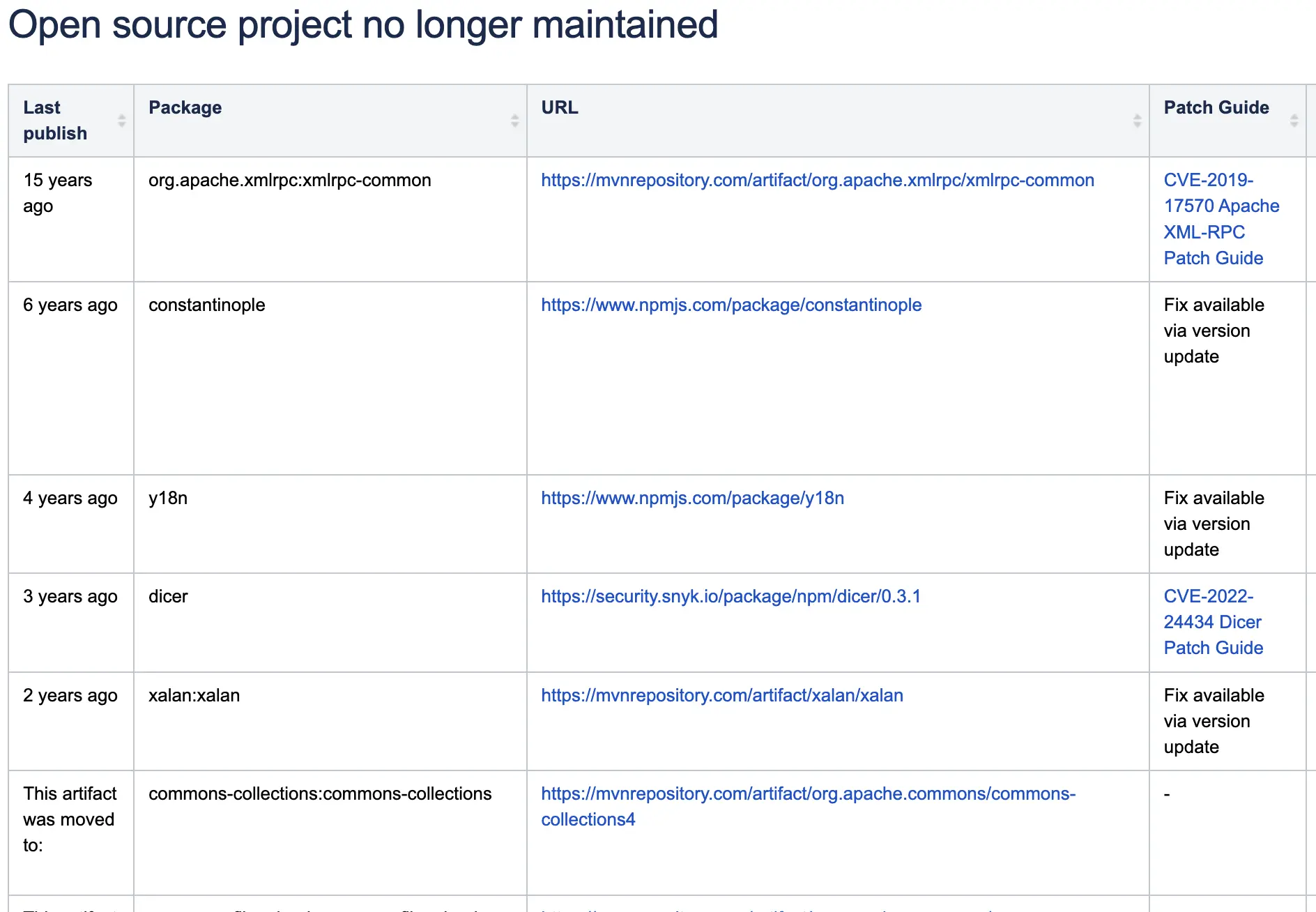
How I Turned 228 Endpoints into 5 Clusters
A practical account of applying dataflow-based clustering to a real codebase — reducing 228 endpoints to 5 reviewable clusters, and finding an RCE chain in the cross-section.
Why Account Takeover Never Ends — Dismantling the ATO Supply Chain
How Korea’s CaaS supply chain reproduces itself through the recycling loop of points, gift cards, and crypto — and why defending against it requires reading the entire behavioral network, not just the login page.
Structure Builders Will Outlast Vulnerability Finders
18 years of vulnerability hunting distilled into one insight: the shift from individual instinct to scalable structure — and what AI means for those left standing.
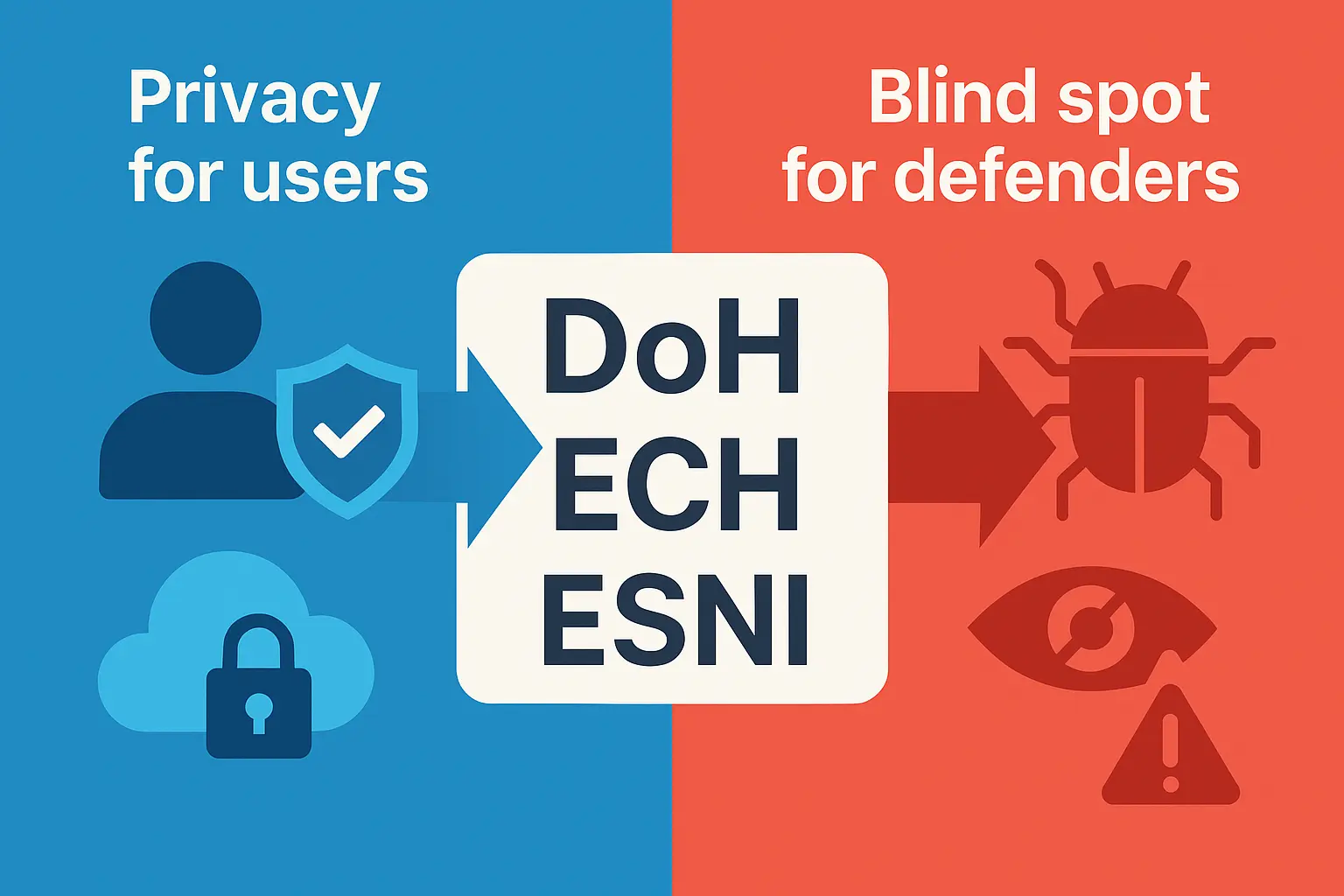
The CAPTCHA That Became a Free Automatic Door for Hackers — A Bypass PoC and Defense Strategy
A practical look at an audio CAPTCHA bypass PoC built with Playwright, Whisper, and Page-Agent, plus the login defenses that still matter after CAPTCHA falls.
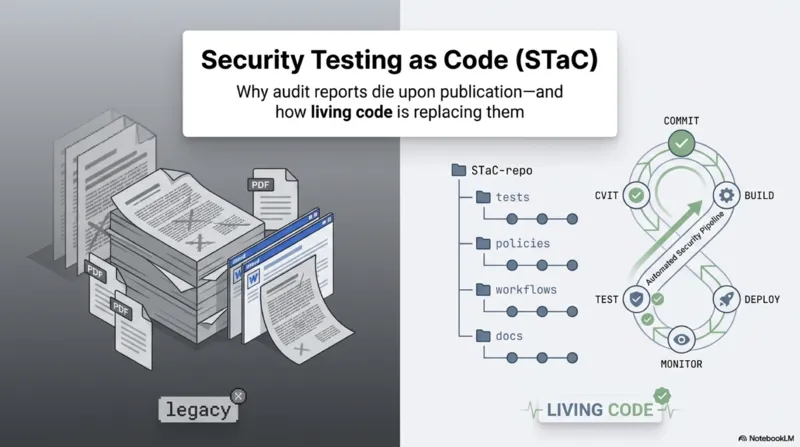
Security Diagnostics Reports Die Upon Publication
We point out the limitations of traditional security diagnostic reports and share the necessity and practical application cases of ‘Security Testing as Code’, managing diagnostic results not as ‘documents’ but as ’executable code (PoC)’.
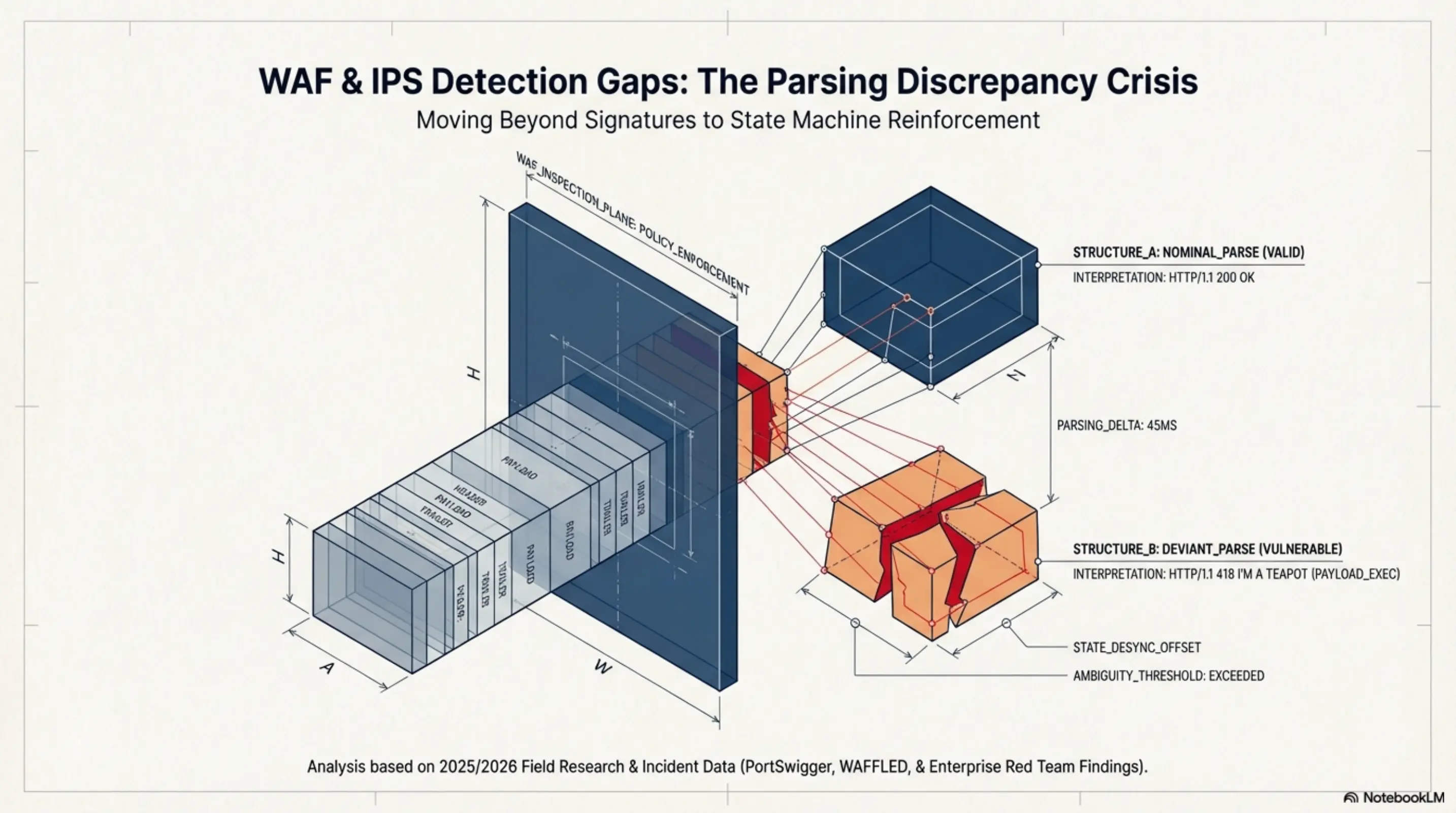
WAF/IPS/IDS Detection Gap Analysis and Remediation Direction
Structural analysis of WAF, IPS, and IDS detection gaps from parsing discrepancies, with a practical remediation taxonomy.
Contracts vs Security Governance — Contracts Enforce. Governance Decides.
Why security governance must drive decisions before contracts enforce them—a structural reframing for security leadership.
eIDAS 2.0 vs. Korea’s Digital Identity System: A Comparative Analysis
Comparative analysis of EU eIDAS 2.0 wallet-based identity and Korea’s mobile ID system across governance, privacy, and operations.